The rise of Call Bomber and SMS Bomber tools has transformed from a niche internet prank into a sophisticated, global cybersecurity threat. By early 2026, these tools will have evolved from simple scripts into high-performance, cross-platform applications used for digital harassment, corporate sabotage, and financial fraud.
This article provides an in-depth analysis of the technical architecture, legal status, and safety risks associated with these tools.
1. What are Call Bomber Tools?
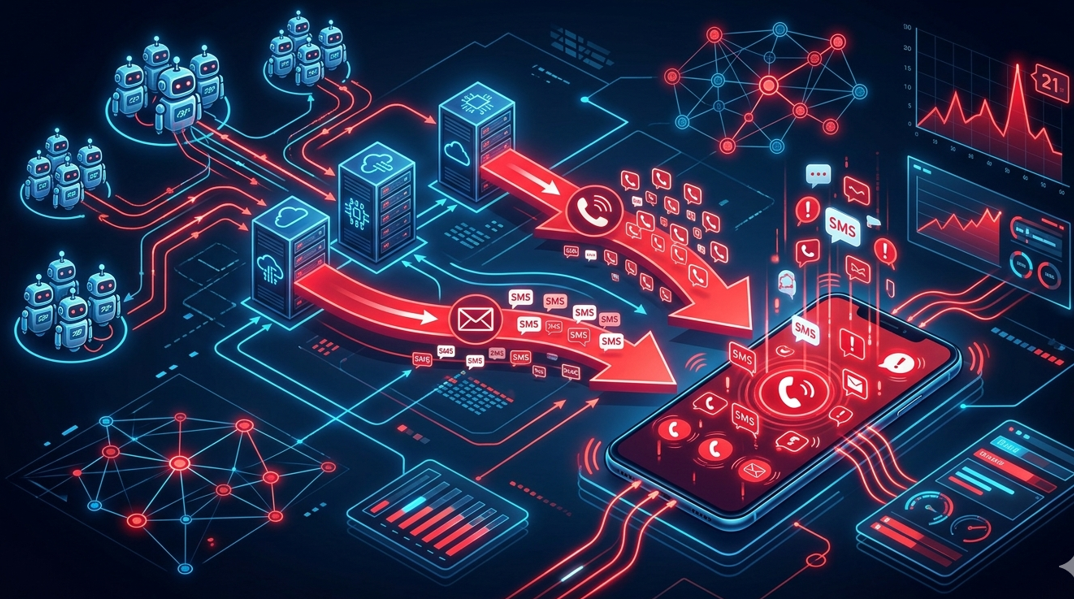
A Call Bomber (or SMS Bomber) is a software tool or web service designed to overwhelm a specific phone number with a massive volume of automated voice calls or text messages in a very short period.
How they Function
Modern tools in 2026 do not send messages in the traditional sense. Instead, they exploit vulnerable APIs of legitimate organizations.
- API Abuse: The tools identify websites that send One-Time Passwords (OTPs) or verification calls (e.g., e-commerce logins, bank authentications, or newsletter signups).
- Mass Requests: The tool sends thousands of fake "Forgot Password" or "Sign Up" requests using the victim's phone number.
- Result: The victim receives hundreds of legitimate calls and texts from trusted brands like Amazon, Google, or local banks, making it impossible to block the "sender" without blocking essential services.
2. Who Developed These Tools?
There is no single creator of call bombers. Instead, they are the product of a decentralized, evolving ecosystem:
- Early Origins (2010s): The first iterations were simple Python scripts shared on forums like GitHub and Pastebin. These were often developed by amateur coders as "proof of concept" experiments in API exploitation.
- Commercial Era (2020-2024): Developers in Eastern Europe, India, and Southeast Asia began "productizing" these scripts. They created user-friendly web interfaces and Telegram bots, charging small fees (in cryptocurrency) for "VIP" bombing services that could bypass standard spam filters.
- Technical Maturation (2025-2026): According to recent cybersecurity reports from firms like Cyble, modern bombers are now written in high-performance languages like Go (Golang) using libraries like FastHTTP. These versions are optimized for speed, allowing a single attacker to hit thousands of endpoints simultaneously.
3. Why Call Bombers Are Not Safe
Using these tools—even "just for a prank"—poses severe risks to both the target and the user.
A. Risks to the Target
- Device Malfunction: The sheer volume of incoming data can cause smartphones to overheat, lag, or completely freeze, requiring a factory reset.
- Security "Smokescreen": This is the most dangerous use-case. Hackers use a "Call Bomb" to distract a victim while they perform a real attack. While the victim is busy deleting hundreds of spam texts, they miss a legitimate "Password Changed" alert or a "SIM Swap" notification.
- Psychological Impact: Continuous notification flooding causes high levels of anxiety and sleep disruption, and can be used as a tool for stalking or domestic abuse.
B. Risks to the User (The Attacker)
- Data Harvesting: Most free call bomber websites are honeypots. When you enter a "target" number and your own details to "start" a bomb, the site owners harvest those numbers. You and your friends are then added to global spam and scam databases.
- Malware Injection: Downloadable ".exe" or ".apk" versions of these tools often contain trojans or info-stealers. While the tool "bombs" your target, it is simultaneously stealing your browser passwords and crypto keys.
4. Global Legal Status & Bans
In 2026, the legal net is tightening around automated harassment tools.
International Treaties
The United Nations Convention against Cybercrime (2024) serves as the global framework. It mandates that member states criminalize "the intentional and without right hindrance of the functioning of a computer system" (which includes phone networks).
Specific Country Actions
- India: One of the most active regions for these tools. Under the Information Technology Act, using or developing these tools is a punishable offense. The government has banned hundreds of "SMS Bomber" domains and Telegram channels.
- Russia: In late 2025, Russia introduced bans on incoming international calls from "unfriendly countries" to combat phone fraud, effectively limiting the reach of international call-bombing services.
- United States & UK: These tools fall under "Harassment" and "Computer Misuse" laws. In the US, the FCC has implemented strict "STIR/SHAKEN" protocols that help carriers identify and drop automated "bomb" traffic before it reaches the handset.
- Banned Countries: Most developed nations have "barred lists" for international calling destinations (such as Afghanistan, Iran, and North Korea) to prevent high-cost fraud often associated with these tools.
5. Summary Table: The State of Call Bombing (2026)
|
Feature |
Description |
|
Primary Method |
Exploitation of legitimate OTP/Verification APIs. |
|
Common Languages |
Go, Python, Node.js. |
|
Legal Status |
Illegal in most countries under Cyber-Harassment or Computer Misuse acts. |
|
Top Risk |
Used as a distraction for financial theft (SIM swapping). |
|
Protection |
Use "DND" (Do Not Disturb) mode and third-party spam filters. |
A Developer’s Guide to Thwarting API Exploitation and Call Bomber Attacks

The surge in API exploitation by call and SMS bombers in 2026 highlights a critical security gap: public-facing endpoints without stateful protection.
If you own a platform that sends OTPs or verification calls, your API is likely already on a "target list" used by these automated tools. Here is the technical roadmap to hardening your infrastructure.
1. Implement Multi-Layer Rate Limiting
Simple rate limiting is no longer enough. You need a tiered strategy to distinguish between a busy user and an automated script.
- Per-IP Limiting: Restrict requests from a single IP to a maximum of 5 OTPs per hour.
- Per-Phone Limiting: This is the most effective defense. Limit a specific phone number to 3 requests per 15 minutes.
- Global Throttling: If your server sees a 300% spike in OTP requests globally, trigger a "High-Alert" mode that automatically increases security challenges for all users.
2. Move to Dynamic reCAPTCHA v3
Many bomber tools in 2026 exploit "invisible" CAPTCHAs that use static site keys.
- Action: Upgrade to reCAPTCHA v3 with a custom score threshold.
- Challenge Escalation: If a request has a low "human" score, do not just block it—force a manual Turnstile or hCaptcha challenge. Automated scripts are designed for speed; a 10-second manual delay breaks their execution loop.
3. Number Intelligence & Validation
Before your server calls an SMS gateway (which costs you money), run a "pre-flight" check on the number:
- Carrier Lookup: Block known VoIP providers (like Google Voice, Twilio, or TextNow) from receiving OTPs if your security model allows it. Most bombers use these because they are free.
- Disposable Detection: Use a real-time API to block "Temporary SMS" numbers.
- Geo-Fencing: If 90% of your users are in Pakistan, but you see a sudden burst of requests for numbers in Eastern Europe, block that traffic at the gateway level.
4. Use WAF (Web Application Firewall) Rules
Configure your WAF (AWS WAF, Cloudflare, or Azure) to identify the specific "fingerprint" of bomber traffic:
- User-Agent Filtering: Many scripts use outdated or "headless" browser signatures. Block any request that doesn't match a modern mobile or desktop browser.
- Behavioral Analysis: Look for "Bursty" patterns—10 requests in 2 seconds followed by 10 seconds of silence. This is a classic hallmark of a bot loop.
5. Backend Logic: The Cooldown Strategy
Hardcode a mandatory 60-second cooldown between requests for the same number at the database level.
- The Trap: If a user (or bot) attempts a second request within that 60 seconds, do not return an error. Return a "Success" message to the client, but do not trigger the API call to your SMS provider. This tricks the bot into thinking the attack is working while saving your API credits and protecting the victim.
Summary Checklist for Developers
|
Security Layer |
Recommended Setting (2026) |
|
IP Rate Limit |
Max 10 requests / 1 hour |
|
Phone Rate Limit |
Max 3 requests / 15 minutes |
|
CAPTCHA |
Dynamic (Score < 0.5 triggers manual check) |
|
Cooldown |
Mandatory 60-90 seconds between hits |
|
Validation |
Block VoIP and Temporary numbers |
Conclusion
Call bomber tools are no longer "harmless pranks." They are a sophisticated form of Denial of Service (DoS) attack on a personal level. As telecommunications providers and governments continue to collaborate through the UN Cybercrime Convention, the technical window for these attacks is closing. For users, the message is clear: interacting with these tools is a fast track to either legal trouble or personal data theft.

Leave a Comment
No comments yet. Be the first to comment!